SAFER
|
|
- This article is about the encryption algorithm. For the SAFER unit used on spacewalks, see Simplified Aid for EVA Rescue.
In cryptography, SAFER (Secure And Fast Encryption Routine) is the name of a family of block ciphers designed primarily by James Massey (one of the designers of IDEA) on behalf of Cylink Corporation. The early SAFER K and SAFER SK designs share the same encryption function, but differ in the number of rounds and the key schedule. More recent versions — SAFER+ and SAFER++ — were submitted as candidates to the AES process and the NESSIE project respectively. All of the algorithms in the SAFER family are unpatented and available for unrestricted use.
| Contents |
SAFER K and SAFER SK
The first SAFER cipher was SAFER K-64, published by Massey in 1993, with a 64-bit block size. The "K-64" denotes a key size of 64 bits. There was some demand for a version with a larger 128-bit key, and the following year Massey published such a variant incorporating new key schedule designed by the Singapore Ministry for Home affairs: SAFER K-128. However, both Lars Knudsen and Sean Murphy found minor weaknesses in this version, prompting a redesign of the key schedule to one suggested by Knudsen; these variants were named SAFER SK-64 and SAFER SK-128 respectively — the "SK" standing for "Strengthened Key schedule", though the RSA FAQ reports that, "one joke has it that SK really stands for 'Stop Knudsen', a wise precaution in the design of any block cipher". Another variant with a reduced key size was published, SAFER SK-40, to comply with 40-bit export restrictions.
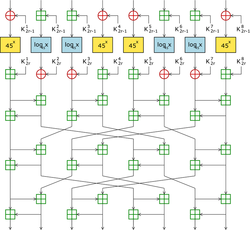
All of these ciphers use the same round function consisting of four stages, as shown in the diagram: a key-mixing stage, a substitution layer, another key-mixing stage, and finally a diffusion layer. In the first key-mixing stage, the plaintext block is divided into eight 8-bit segments, and subkeys are added using either addition modulo 256 (denoted by a "+" in a square) or XOR (denoted by a "+" in a circle). The substitution layer consists of two S-boxes, each the inverse of each other, derived from discrete exponentiation (45x) and logarithm (log45x) functions. After a second key-mixing stage there is the diffusion layer: a novel cryptographic component termed a Pseudo-Hadamard Transform (PHT). (The PHT was also later used in the Twofish cipher.)
SAFER+ and SAFER++
There are two more-recent members of the SAFER family that have made changes to the main encryption routine, designed by the Armenian cryptographers Gurgen Khachatrian and Melsik Kuregian in conjunction with Massey.
- SAFER+ (Massey et al, 1998) was submitted as a candidate for the Advanced Encryption Standard and has a block size of 128 bits. The cipher was not selected as a finalist. SAFER+ was included in the Bluetooth standard as an algorithm for authentication and key generation.
- SAFER++ (Massey et al, 2000) was submitted to the NESSIE project in two versions, one with 64 bits, and the other with 128 bits.
See also
References
- Alex Biryukov, Christophe De Cannière, Gustaf Dellkrantz: Cryptanalysis of SAFER++. CRYPTO 2003: 195-211
- Lars R. Knudsen: A Detailed Analysis of SAFER K. J. Cryptology 13(4): 417-436 (2000)
- James L. Massey: SAFER K-64: A Byte-Oriented Block-Ciphering Algorithm. Fast Software Encryption 1993: 1-17
- James L. Massey: SAFER K-64: One Year Later. Fast Software Encryption 1994: 212-241
- James Massey, Gurgen Khachatrian, Melsik Kuregian, Nomination of SAFER+ as Candidate Algorithm for the Advanced Encryption Standard (AES)
- Massey, J. L., "Announcement of a Strengthened Key Schedule for the Cipher SAFER", September 9, 1995.
- James Massey, Gurgen Khachatrian, Melsik Kuregian, "Nomination of SAFER++ as Candidate Algorithm for the New European Schemes for Signatures, Integrity, and Encryption (NESSIE)," Presented at the First Open NESSIE Workshop, November 2000.
- Lars R. Knudsen: A Key-schedule Weakness in SAFER K-64. CRYPTO 1995: 274-286
- Lars R. Knudsen, Thomas A. Berson: Truncated Differentials of SAFER. Fast Software Encryption 1996: 15-26
- Nomination of SAFER+ as Candidate Algorithm for the Advanced Encryption Standard (AES), Submission document from Cylink Corporation to NIST, June 1998.
External links
- John Savard's description of SAFER+ (http://home.ecn.ab.ca/~jsavard/crypto/co040407.htm)
- John Savard's description of SAFER K and SAFER SK (http://home.ecn.ab.ca/~jsavard/crypto/co040301.htm)
- SCAN's entry for SAFER K (http://www.users.zetnet.co.uk/hopwood/crypto/scan/cs.html#SAFER-K)
- SCAN's entry for SAFER SK (http://www.users.zetnet.co.uk/hopwood/crypto/scan/cs.html#SAFER-SK)
- SCAN's entry for SAFER+ (http://www.users.zetnet.co.uk/hopwood/crypto/scan/cs.html#SAFER+)
- SCAN's entry for SAFER++ (http://www.users.zetnet.co.uk/hopwood/crypto/scan/cs.html#SAFER++)
- Announcement of new key schedule (SAFER SK) (http://groups.google.com/groups?selm=4336pm%24e9t%40net.auckland.ac.nz)
| Block ciphers edit (https://academickids.com:443/encyclopedia/index.php?title=Template:Block_ciphers&action=edit) |
| Algorithms: 3-Way | AES | Akelarre | Blowfish | Camellia | CAST-128 | CAST-256 | CMEA | DEAL | DES | DES-X | FEAL | FOX | FROG | G-DES | GOST | ICE | IDEA | Iraqi | KASUMI | KHAZAD | Khufu and Khafre | LOKI89/91 | LOKI97 | Lucifer | MacGuffin | Madryga | MAGENTA | MARS | MISTY1 | MMB | NewDES | RC2 | RC5 | RC6 | REDOC | Red Pike | S-1 | SAFER | SEED | Serpent | SHACAL | SHARK | Skipjack | Square | TEA | Triple DES | Twofish | XTEA |
| Design: Feistel network | Key schedule | Product cipher | S-box | SPN Attacks: Brute force | Linear / Differential cryptanalysis | Mod n | XSL Standardisation: AES process | CRYPTREC | NESSIE Misc: Avalanche effect | Block size | IV | Key size | Modes of operation | Piling-up lemma | Weak key |