Blowfish (cipher)
|
|
| Blowfish | |||
| |||
| General | |||
| Designer(s) | Bruce Schneier | ||
| First published | 1993 | ||
| Derived from | - | ||
| Cipher(s) based on this design | - | ||
| Algorithm detail | |||
| Block size(s) | 64 bits | ||
| Key size(s) | 32-448 bits in steps of 8 bits; default 128 bits | ||
| Structure | Feistel network | ||
| Number of rounds | 16 | ||
| Best cryptanalysis | |||
| Four rounds of Blowfish are susceptible to a second-order differential attack (Rijmen, 1997); for a class of weak keys, 14 rounds of Blowfish can be distinguished from a random permutation (Vaudenay, 1996). | |||
In cryptography, Blowfish is a keyed, symmetric block cipher, designed in 1993 by Bruce Schneier and included in a large number of cipher suites and encryption products. While no effective cryptanalysis of Blowfish has been found to date, more attention is now given to block ciphers with a larger block size, such as AES or Twofish.
Schneier designed Blowfish as a general-purpose algorithm, intended as a replacement for the aging DES and free of the problems associated with other algorithms. At the time, many other designs were proprietary, encumbered by patents or kept as government secrets. Schneier has stated that, "Blowfish is unpatented, and will remain so in all countries. The algorithm is hereby placed in the public domain, and can be freely used by anyone."
Notable features of the design include key-dependent S-boxes and a highly-complex key schedule.
| Contents |
The algorithm
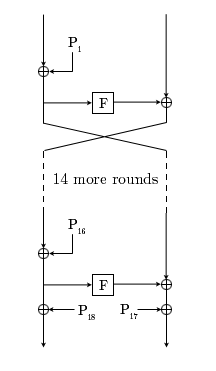
Blowfish has a 64-bit block size and a key length of anywhere from 32 bits to 448 bits. It is a 16-round Feistel cipher and uses large key-dependent S-boxes. It is similar in structure to CAST-128, which uses fixed S-boxes.
The diagram to the left shows the action of Blowfish. Each line represents 32 bits. The algorithm keeps two subkey arrays: the 18-entry P-array and four 256-entry S-boxes. The S-boxes accept 8-bit input and produce 32-bit output. One entry of the P-array is used every round, and after the final round, each half of the data block is XORed with one of the two remaining unused P-entries.
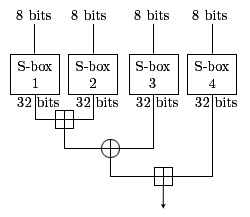
The diagram to the right shows Blowfish's F-function. The function splits the 32-bit input into four eight-bit quarters, and uses the quarters as input to the S-boxes. The outputs are added modulo 232 and XORed to produce the final 32-bit output.
Since Blowfish is a Feistel network, it can be inverted simply by XORing P17 and P18 to the ciphertext block, then using the P-entries in reverse order.
Blowfish's key schedule starts by initializing the P-array and S-boxes with values derived from the hexadecimal digits of pi, which contain no obvious pattern. The secret key is then XORed with the P-entries in order (cycling the key if necessary). A 64-bit all-zero block is then encrypted with the algorithm as it stands. The resultant ciphertext replaces P1 and P2. The ciphertext is then encrypted again with the new subkeys, and P3 and P4 are replaced by the new ciphertext. This continues, replacing the entire P-array and all the S-box entries. In all, the Blowfish encryption algorithm will run 521 times to generate all the subkeys - about 4KB of data is processed.
Cryptanalysis of Blowfish
There is no effective cryptanalysis of Blowfish known publicly as of 2004, although the 64-bit block size is now considered too short, because encrypting more than 232 data blocks can begin to leak information about the plaintext due to a birthday attack. Despite this, Blowfish seems thus far to be secure. While the short block size does not pose any serious concerns for routine consumer applications like e-mail, Blowfish may not be suitable in situations where large plaintexts must be encrypted, as in data archival.
In 1996, Serge Vaudenay found a known-plaintext attack requiring 28r + 1 known plaintexts to break, where r is the number of rounds. Moreover, he also found a class of weak keys that can be detected and broken by the same attack with only 24r + 1 known plaintexts. This attack cannot be used against the full 16-round Blowfish; Vaudenay used a reduced-round variant of Blowfish. Vincent Rijmen, in his Ph.D. thesis, introduced a second-order differential attack that can break four rounds and no more. There remains no known way to break the full 16 rounds, apart from a brute-force search.
In 2005, Dieter Schmidt investigated the Blowfish key schedule and noted that the subkeys for the third and fourth round are independent of the first 64 bits of the user key [1] (http://eprint.iacr.org/2005/063).
Blowfish in practice
Blowfish is one of the faster block ciphers in widespread use, except when changing keys. Each new key requires pre-processing equivalent to encrypting about 4 kilobytes of text, which is very slow compared to other block ciphers. This prevents its use in certain applications, but is not a problem in others. In one application, it is actually a benefit: the password-hashing method used in OpenBSD uses an algorithm derived from Blowfish that makes use of the slow key schedule; the idea is that the extra computational effort required gives protection against dictionary attacks.
In some implementations, Blowfish has a relatively large memory footprint of just over 4 kilobytes of RAM. This is not a problem even for older smaller desktop and laptop computers, but it does prevent use in the smallest embedded systems such as early smartcards.
Blowfish is not subject to any patents and is therefore freely available for anyone to use. This has contributed to its popularity in cryptographic software.
See also
References
- V. Rijmen, "Cryptanalysis and design of iterated block ciphers", Doctoral dissertation, October 1997.
- Bruce Schneier, Description of a New Variable-Length Key, 64-bit Block Cipher (Blowfish). Fast Software Encryption 1993: 191-204 [2] (http://www.schneier.com/paper-blowfish-fse.html).
- Bruce Schneier, The Blowfish Encryption Algorithm -- One Year Later, Dr. Dobb's Journal, 20(9), p. 137, September 1995 [3] (http://www.schneier.com/paper-blowfish-oneyear.html).
- S. Vaudenay, "On the weak keys of Blowfish," Fast Software Encryption (FSE'96), LNCS 1039, D. Gollmann, Ed., Springer-Verlag, 1996, pp. 27--32.
External links
- Official Blowfish website (http://www.schneier.com/blowfish.html)
- List of Blowfish users (http://www.schneier.com/blowfish-products.html)
- SCAN's entry for Blowfish (http://www.users.zetnet.co.uk/hopwood/crypto/scan/cs.html#Blowfish)
- Blowfish JavaScript implementation (http://aam.ugpl.de/node/1060)
- Blowfish PHP implementation (http://php-einfach.de/sonstiges_generator_blowfish.php)
| Block ciphers edit (https://academickids.com:443/encyclopedia/index.php?title=Template:Block_ciphers&action=edit) |
| Algorithms: 3-Way | AES | Akelarre | Blowfish | Camellia | CAST-128 | CAST-256 | CMEA | DEAL | DES | DES-X | FEAL | FOX | FROG | G-DES | GOST | ICE | IDEA | Iraqi | KASUMI | KHAZAD | Khufu and Khafre | LOKI89/91 | LOKI97 | Lucifer | MacGuffin | Madryga | MAGENTA | MARS | MISTY1 | MMB | NewDES | RC2 | RC5 | RC6 | REDOC | Red Pike | S-1 | SAFER | SEED | Serpent | SHACAL | SHARK | Skipjack | Square | TEA | Triple DES | Twofish | XTEA |
| Design: Feistel network | Key schedule | Product cipher | S-box | SPN Attacks: Brute force | Linear / Differential cryptanalysis | Mod n | XSL Standardisation: AES process | CRYPTREC | NESSIE Misc: Avalanche effect | Block size | IV | Key size | Modes of operation | Piling-up lemma | Weak key |